CrowdStrike Holdings
One subscriber to this Substack wrote to me and said he likes the company reports but the companies featured have all been successful for at least a couple of decades and the high returns are in the rear-view mirror. He asked me to look at younger companies whose phase of high growth, and the consequential high share price appreciation, is still in the future.
“By the time everyone calls it a great business, the exceptional returns are usually in the rearview. The time to buy is when it is misunderstood, undiscovered and under-appreciated.”
Ian Cassel- The Microcap Club
It is a fair point. I have a preference for industries where the market structure is quite stable and not heavily contested. I also prefer companies whose business models have proved to be profitable over a few cycles. This means giving up on high early returns but also reduces risk of failure. Finding and investing in growth companies at a much earlier stage could be more profitable but is more risky as the risk of failure is higher. It is a difficult balancing act between risk and reward.
CrowdStrike was formed in 2012 but its IPO was in June 2019. It is the kind of stock which might appeal more to my correspondent. It is focused on Cybersecurity.
Introduction
As the internet has grown exponentially, there has been much less attention paid to the robustness and security features underlying the whole system. In his piece on CRWD, the writer at Mostly Borrowed Ideas (MBI) starts with a quote from an NYT opinion piece which I reproduce below:
In a NY Times opinion piece in 2018, Zeynep Tufekci wrote, “The early Internet was intended to connect people who already trusted one another, like academic researchers or military networks. It never had the robust security that today’s global network needs. As the Internet went from a few thousand users to more than three billion, attempts to strengthen security were stymied because of cost, shortsightedness and competing interests. Connecting everyday objects to this shaky, insecure base will create the Internet of Hacked Things. This is irresponsible and potentially catastrophic.”
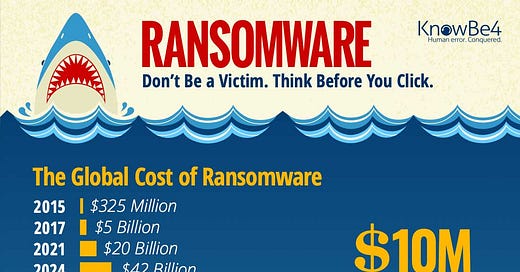
Internet Security is a big problem. The problem is growing in complexity and scope. A recent report in Cybercrime magazine suggested that Ransomware costs are likely to grow to $ 265bn by 2031.
The graphic above shows the growth in the cost of Ransomware. Source: KnowBe4
CNA Financial, a Chicago-based insurance company paid $40 million USD to Russian cybercriminals in the largest recorded Ransomware payout. Just in the last few days, MGM Casinos have been the subject of Ransomware attacks.
In fact since I began researching this article, I have noticed news outlets seem to be chock full of stories of hacking, malware, security lapses, identity theft, security breaches, phising scams, ransomware incidents and so on. The problem seem to be growing fast. Global average weekly cyber attacks rose 8% in the second quarter of 2023, according to Check Point Research, with the average number of attacks per organization per week hitting a two-year high.
These are all elements of vast, rapidly evolving issue which is difficult to understand for a non-specialist. This report will, of necessity, be full of technical jargon. Wherever possible, I have tried to avoid jargon and where it is unavoidable, i have attempted to explain it. There is a greater than usual real risk that I have misunderstood some key elements of the topic.
I have read various articles and papers on the subject including CrowdStrike’s 2023 Global Threat Report which can be found here. Anybody who reviews this material is likely to come to the conclusion that Computers network attacks are only likely to increase significantly and companies, governments and other organizations will have to increase their investments in cybersecurity measures.
Introduction to Network Security
When computer networking and the internet became commonplace in the mid-1990s onwards, the first two elements of security were a Firewall and Antivirus software.
A Firewall can be defined as a network security device whose function is to monitor and filter incoming and outgoing network traffic based on the predefined security policies established by an organization to protect it from any unethical practices. A firewall acts as a barrier between a private internal network and the public Internet. It should allow non-threatening traffic in and keep dangerous traffic out of the network.
The first network firewalls were invented in the late 1980s and were simple packet filters that allowed or denied traffic based on the source and destination IP addresses and ports.
In the 1990s, they became more sophisticated. They tracked the state of connections and make more informed decisions about whether to allow or deny traffic. They also incorporated other security features, such as intrusion detection and prevention systems. More recently firewalls have become more software based as they have moved to the cloud-based and become virtual. They are now evolving to meet new threats such as such as ransomware and the distributed denial-of-service attacks favoured by state-backed hackers .
Firewalls are an important part of network security, but need to be supplemented with others such as antivirus software, strong passwords, user education etc. Firewalls try to block malicious traffic from reaching a computer, while antivirus software removes malware that has already infected a computer.
Endpoint Security
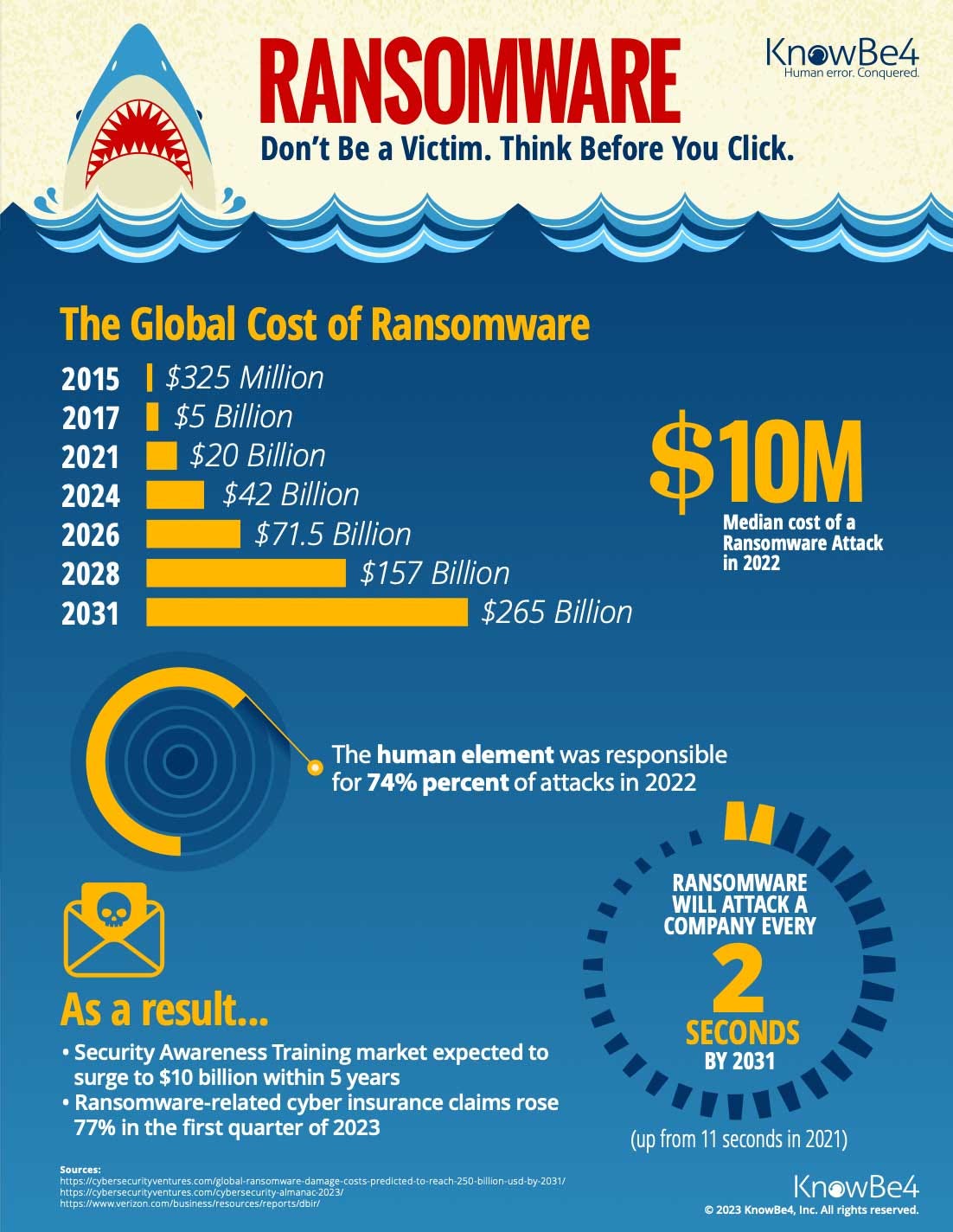
CRWD’s core business is in Endpoint security. An Endpoint is any device which can be connected to a network. Thirty years ago, that would have meant desktops used by workers in cubicles on company premises whose PCs were connected to the company network and perhaps the internet. Today, there are many other ways to connect to networks such as mobile phones, tablets, notebooks, security cameras, Point of Sales (PoS) systems, and numerous other Internet of Things (IoT) devices. The graph below was produced by Mary Meeker in 2019 and it shows the type of endpoints that a modern network might have. There are many different types of endpoints and they are more geographically spread.
We need to start by defining Malware. Malware is a malicious software in a system/network that enables access to sensitive information for sabotage or espionage through methods such as attachments and phising
In 1987, McAfee launched its first antivirus (AV) solutions and four year later they were followed by Symantec’s effort. These two companies are part of a larger group, collectively known as legacy players. Trend Micro, Sophos and Kaspersky are other legacy players.
The aim of these antivirus products was to prevent malware from entering networks through endpoints. In the early days AV worked by signature-based detection. It could only protect a system/network against malware attacks that had previously been identified as malicious and stored in a database.
AV relies on a database of known malware signatures. A signature is a unique pattern of bytes that is associated with a particular piece of malware. When a signature-based scanner detects a file that matches a known signature, it will flag the file as malicious.
Signature-based detection was used in a number of ways:
Anti-malware software: Anti-malware software uses signature-based detection to identify and remove known malware from computers.
Intrusion detection systems (IDSs): IDSs use signature-based detection to identify malicious traffic on networks.
Firewalls: Firewalls can use signature-based detection to block malicious traffic from reaching computers.
Signature-based detection is an effective way to detect known malware and probably worked well enough before 2003.
However, bad actors are constantly creating new malware that does not match any known signatures. This is known as zero-day malware and it cannot be detected by signature-based detection.
To address this limitation, signature-based scanners are often updated with new signatures on a regular basis. This hopefully means they can detect the latest malware threats.
However by around 2003-2007, it was clear the rate of production of malware was so high, that updates just could not happen fast enough.
Signature-based detection was augmented by other detection methods, such as:
Heuristic detection: This method uses algorithms to identify suspicious activity, even if it does not match a known signature.
Behavior-based detection: This method monitors the behavior of a file or process to identify malicious activity.
Machine learning: This method uses artificial intelligence to learn to identify malicious activity.
CrowdStrike Holdings
CrowdStrike was formed in 2012 and their aim was to take a very different approach to the legacy players. They wanted to build the first “Security Cloud platform” .
The story of the founding is as follows: George Kurtz was the CTO of McAfee and he was on a plane when he watched a fellow passenger waiting for 15 minutes as McAfee scanned the laptop for viruses. Mr. Kurtz thought there had to be a better to secure laptops or other mobile devices to networks. He put together a 25-slide deck to pitch CrowdStrike to Warburg Pincus. He received $25mn seed money. He later observed this was $1mn per slide and regretted not putting together a much larger presentation!
CrowdStrike took a new approach from the legacy companies. They leveraged the network effects of crowdsourced data applied to modern technologies such as AI, cloud computing, and graph databases.
They built the Falcon Platform to detect threats and stop breaches. It is comprised of two integrated technologies:
A Lightweight agent and
A Threat Graph.
Falcon Platform now is a series of tightly interconnected applications that offer the customer more than just improved security - it also has better visibility and the opportunity to simplify and consolidate historically complicated and cumbersome functions.
For many years companies tended to buy products to meet new threats as they emerged and ended up with a hodgepodge of products from various suppliers which may be the “best in class” for specific problems but worked imperfectly as a complete security solution.
Many entities are now looking to reduce the number of vendors drastically and focus on those few suppliers who can offer a full-suite or “platform” solution.
How does the CrowdStrike Product work?
A local device is installed at each endpoint (on Desktops, mobile phones, tablets etc.) and it provides protection but also gathers data which is sent to a central unit which uses AI/ML to analyse the output. A large company or organisation may have tens of thousands of such devices.
The local device is also known as single lightweight agent (~35 MB). It intelligently collects and streaming high fidelity data to the Falcon platform for real-time decision-making.
“We believe our approach has defined a new category called the Security Cloud, which has the power to transform the cybersecurity industry the same way the cloud has transformed the customer relationship management, human resources, and service management industries.”
“Using cloud-scale AI, our Security Cloud enriches and correlates trillions of cybersecurity events per week with indicators of attack, threat intelligence and enterprise data (including data from across endpoints, workloads, identities, IT assets and configurations) to create actionable information, identify shifts in adversary tactics and automatically detect and prevent threats in real-time across our customer base. The more data that is fed into our Falcon platform, the more intelligent our Security Cloud becomes, and the more our customers benefit, creating a powerful network effect that increases the overall value we provide”
There is a network effect at work as many users’ data is continuously fed to a central platform which spots threat patterns and acts to benefit all users.
Adding multiple agents on an endpoint device reduces performance and requires increased management effort. If you buy many products from different suppliers, you would have to have multiple lightweight devices on each endpoint.
As CRWD modules only require one agent, you don’t need to install multiple agents for each different CRWD security module. This is an important incentive against mixing and matching suppliers.
The sales process can happen seamlessly without any active interaction with the sales resource at CRWD. If you use one CRWD module, you can easily sign up for any other module for 15-day trial on your own. Sales of additional models have a very high margin.
“..the beauty of the model is after you purchase your first module, every module after that is virtually 100% gross margin. And so obviously, the more modules we have, the more opportunity to enhance our gross margin. And you've seen the adoption rates from our earnings call, when we have 4, 5 or 6 modules bought by the customers in over 60%, 40% and over 20%, respectively. And that's exciting for us. All of those have been growing. And at some point, we're going to be dropping how many of our customers have 4 or more because it's going to get closer and closer to that 100%, and you will only be talking about 5, 6 and 7. And then similarly, we're going to drop 5 at some point. And we talk about 6, 7, 8. So those are the things that really get us excited…”
“The percentage of customers who adopted four or more modules increased from literally zero percentage in FY’17 to 64% in 1Q’22. In fact, 50% subscribers have adopted >5 modules, and 27% did >6 modules.”
The huge volumes of data generate by the lightweight agents goes to the Falcon Platform and is analysed by the Threat Graph.
“Our Threat Graph processes, correlates, and analyzes this data in the cloud using a combination of AI and behavioral pattern-matching techniques. By analyzing and correlating information across our massive, crowdsourced dataset, we are able to deploy our AI algorithms at cloud-scale and build a more intelligent, effective solution to detect threats and stop breaches that on-premise or single instance cloud products cannot match.”
The scale of the data being handled is huge.
“We handle 4 trillion events per week. These are signals that come into our platform, right? We have one of the largest Kafka clusters in the world. So we're competing with the Facebooks and the Googles, et cetera, for talent just because of the sheer scale that we operate in. 4 trillion events per week. So as today starts and ends, we will have handled more events in our platform, these signals that come into our platform that Twitter has tweets in an entire year. Just to put that in perspective.”
The legacy solutions were based on a “trust but verify” approach which means once you are verified upon entering the network, you are essentially trusted within the system thereafter.
Those with malicious intent only need work out how to fool the system once. Now “trust but verify” is being increasingly being replaced by the Zero Trust approach. Zero Trust requires users to be authenticated, authorized, and validated before granted access and to be regularly tested thereafter. Zero Trust is discussed later.
The Crowdstrike Modules
Some of the 23 CRWD Modules are listed below:
Falcon Prevent (Next Generation Anti Virus) (Basic core module)
Falcon Device control (Endpoint Device Control/USB Security) (Basic core module)
Falcon Insight (Endpoint Detection and Response) (Basic core module)
Falcon Firewall Management (manage firewall policies ) (Basic core module)
Falcon X (Threat intelligence)
Falcon OverWatch (Managed threat hunting) - A human system plus AI that watches over risk in association with the basic Threat Graph
Falcon Discover (Network Security Monitoring)
Falcon Search Engine (Search across all malware collected by the platform)
Falcon Spotlight (Vulnerability Management)
Falcon sandbox (Analyze malware in a safe environment)
Falcon Complete (managed detection and response)
Falcon CWP (Cloud workload protection)
Falcon Discover for cloud environments
Falcon Identity Threat Detection (prevent golden ticket attacks)
Falcon Zero Trust (additional insight into identities and account directories)
Falcon Horizon (Cloud Security Posture Management)
Falcon forensics (incident response tool for identifying relevant security event data)
Falcon X Recon (additionally threat intelligence from digital sources)
Humio (log management/Extended Detection and Response or XDR)- (Newer More advanced module)
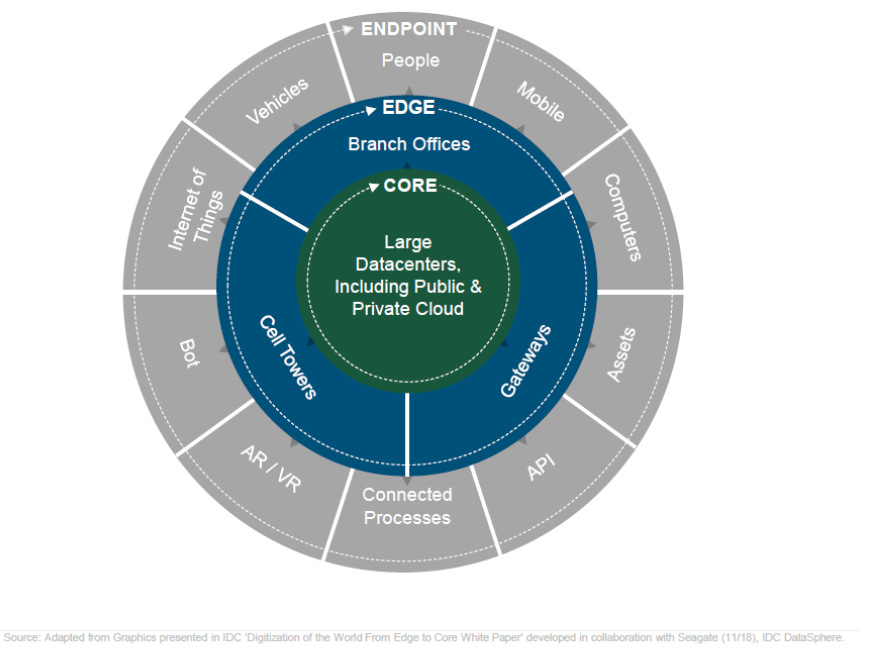
In terms of product packaging, Falcon Platform has five alternatives: Falcon GO, Falcon Pro, Falcon Enterprise, Falcon Elite, and Falcon Complete MDR (see below) .
Falcon Go is the cheapest and includes just two modules (Prevent and Device Control) and costs $ 300 per user per year with a minimum of five devices. Falcon Complete MDR is the most expensive.
Module subscriptions account of about 90% of total revenues. The balance 10% of the revenues come from Professional Services.
Services such as incident response/forensic investigation services, technical assessment and strategic advisory services, and training. These are not very profitable in their own right but often lead to Module sales.
We will now look at the financial performance of the company. We will then try and look various estimates of the Total Addressable Market TAM for the company before considering the structure of the market and the competitor landscape.
The Chart above shows the CRWD chart since the IPO in 2019. The company have given a CAGR return of 29% in 4.25 years.
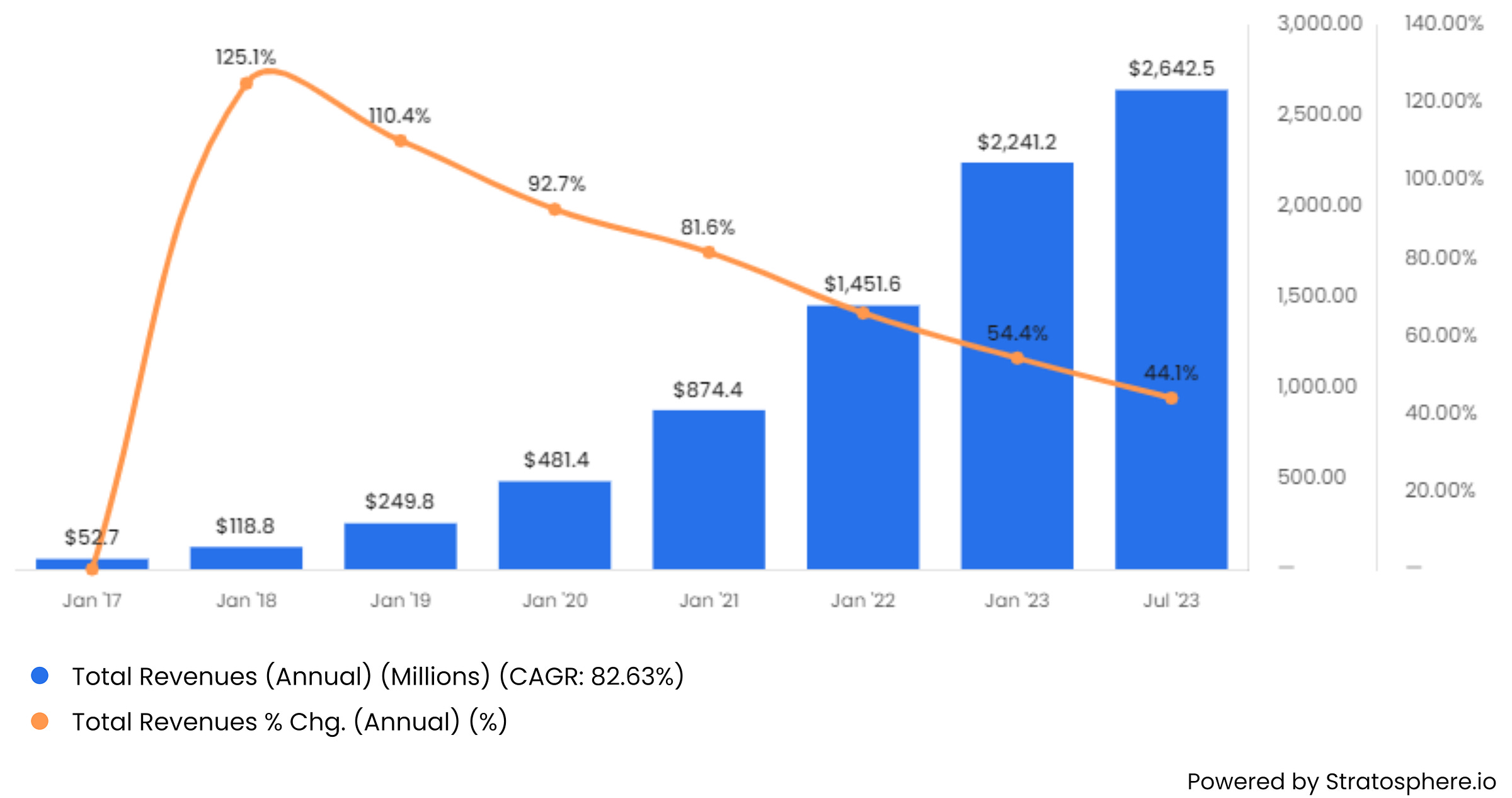
Chart 1: CRWD Annual Revenues and Revenue Growth ($ Millions)
Total Revenues have grown 10x between Jan 2019 and Jan 2023. The annual rate of growth has slowed but is still a notable 44.1%.
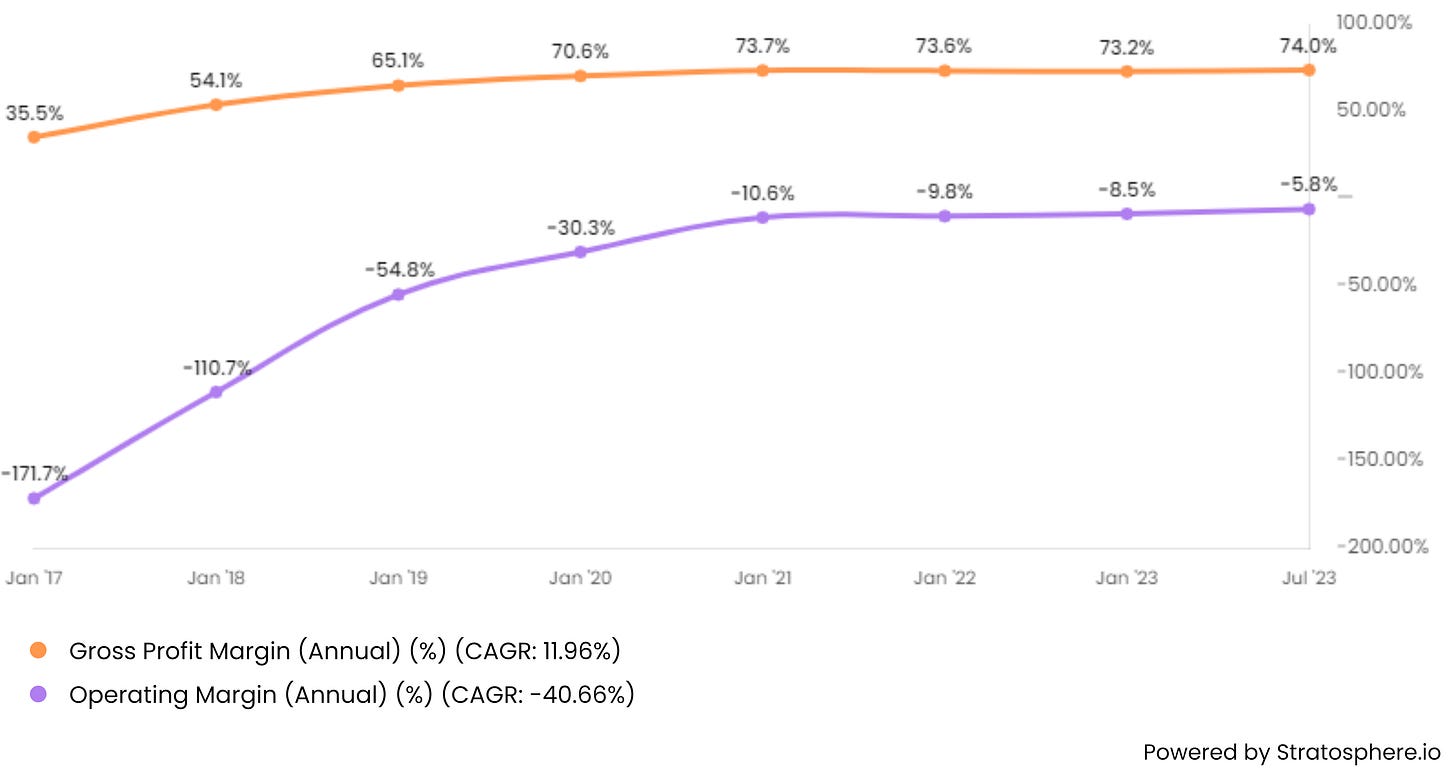
Chart 2: CRWD Operating Profit ($ millions) and Operating Margin (%).
The company has been making an operating loss. For the full year to Jan 2023, it was at -$190mn. Operating margin has improved from -171% to -5.8% currently. The company’s medium-term target for operating margin is +20%.
Chart 3: CRWD Gross Profit Margin (%) and Operating Profit Margin (%).
Gross Margins have increased from 35.5% to 74%. The target is for a Gross Margin of 82% (on a non-GAAP basis) by 2024.
Chart 4: CRWD Quarterly Operating Income and Net Income ($ Millions).
Quarterly operating losses have narrowed. The company made a net profit in the last two quarters thanks to investment and interest income.
Chart 5: CRWD Cash from Operations ($ Millions).
The company has been operating cash flow positive sine 2019/2020 and in the 12 months to Jan 2023, the operating cash flow was $ 941mn.
Chart 6: CRWD Cash from Operations and Free Cash Flow ($ Millions).
Free Cash Flow has also grown strongly, and broadly in line, with Operating Cash Flow.
Chart 7: CRWD Annual Free Cash Flow Margin (%).
The free cash flow margin has risen to 31.9%. The company had a 30% FCF margin as along term target but it has been met for three years in a row.
For fast growing, but not profitable SaaS companies, analysts sometimes use the rule of 60 as a quick check on the health of the underlying trends. The metric is that the sum of sales growth plus free cash flow margin should be more than 60%. For CRWD, it is 44.1% plus 31.9% which is 76%. As sales growth slows, this may fall but will hopefully remain well above 60% before the company reports an operating profit.
Chart 8: CRWD Total Current Assets and Liabilities and Long-Term Debt ($ Millions).
Let us consider the Balance Sheet. Long-term debt has stabilised at ~$ 740mn. Current assets are $ 4bn while current liabilities are only ~ $ 2.2 bn. The positive gap between the two is growing.
Chart 9: CRWD Various Asset Items ($ millions) .
Total assets have grown strong and are currently at ~$ 5.5bn. $ 3.2bn of that is Cash and short-term investments.
Chart 10: CRWD Weighted Average shares outstanding (millions).
There was a major increase in shares due to the IPO in 2019 and a follow-up offering in 2020. Since then shares outstanding have increased due to Stock-Based Compensation (SBC). (See below).
Chart 11: CRWD Stock-Based Compensation (SBC) ($ millions) and SBC as percentage of revenue (%).
The company has been in a growth phase. Cybersecurity engineers are scarce and expensive and cash has to be preserved. Therefore, SBC has been high. In 2022, at $ 527mn, SBC was 72% of total free cash flow generation. We would expect this to fall over time. The company has pledged stock dilution will fall to below 2%-3% per annum going forward.
Chart 12: CRWD Gross Profit and Operating Expenses ($ Millions).
Gross profit is growing faster than expenses so the company is on track to make an operating profit soon. In SaaS Companies, many costs are front-loaded but the revenues accrue over time. These companies spend heavily on R&D and Sales & Marketing upfront, to build out the platform & attract new customers. Customers then add new modules and revenues stream in later on. In other words, the revenues and costs aren't necessarily aligned in time. The losses aren't as extreme as they appear in the quarterly GAAP results
Chart 13: Some summary valuation ratios ($ Millions).
As the company is not profitable at the net income level, we can’t look at historic P/E ratios. Instead, we look at Price to Sales (P/S) and Price to Free Cash Flow (P/FCF) ratios below. Both broadly indicate that the stock is (slowly) getting cheaper over time. Based on 2025 estimated eps, the company is on a forward P/E ratio is 52.7 times.
Long-term Guidance
Management long term guidance is a follows: the long-term aim is 20%+ operating margins. they expect this to be achieved as follows:
Subscription Gross Margin 75-80%+
S&M 30-35%
R&D 15-20%
G&A 7-9%
Operating Margin 20%+
These can be used as the basis for a DCF valuation model for the company. This is an important exercise to be done to try and determine whether the stock is fairly valued at current levels.
How big is the Total Addressable Market (TAM) ?
There are a wide range of estimates for endpoint cybersecurity market TAM. CRWD is moving beyond endpoint security (where it is no. 1) to Cloud Workload Security.
If you use AWS, Azure or GCP as your Cloud Host, they are responsible for the overall security of the Cloud but you are responsible for the security of their workload. It should be noted, the cloud hyperscalers (esp Microsoft) have their own products but customers may resist the implied vendor lock-in, especially if they are following the increasingly common hybrid cloud strategy.
Therefore, the TAM for CRWD should be the sum of the endpoint and cloud workload security market.
Gartner estimated the endpoint security market to be ~$12bn in 2023. Gartner’s estimates for cloud security market is $2.5bn in 2023. If we add the two, the CRWD TAM according to Gartner is $14.5bn in 2023. JP Morgan analysts in 2022 estimated the CRWD TAM to be $10bn and argued it would grow to $ 27bn in three years. We can conclude that the CRWD TAM is likely to be between $10bn and $15bn in 2023.
This compares with CRWD current annual revenue run rate of $ 3bn, so there is plenty of room for CRWD to grow sales.
Sales Strategy
CrowdStrike uses a combination of a direct sales force and channel partners. In 2018, they announced that Falcon Prevent was available for trial and purchase from the AWS Marketplace. This has boosted the the pace of expansion as it extends their reach to customers of all sizes leveraging off Amazon's huge Cloud business and its strong SME portfolio.
In early 2023, CRWD announced a new multifaceted strategic partnership with Dell to deliver the Falcon platform to Dell's customers globally. Purchasers of new Dell Servers can choose to have CRWD devices fitted as part of the specification of the new machine along with a Falcon subscription. The deal also involves Dell using CrowdStrike’s products in the Managed Cybersecurity service business it offers to clients.
One of the largest CRWD customers is CDW -Computer Discount Warehouse, a major distributor with 40% of its customers in the public sector. Public sector entities are often the largest category of targets for hackers. System integrators such as Computacenter and Atos in Europe also account for a significant share of sales.
As of January 2023, CRWD had 23,000 subscription customers compared with about ~5,000 subscribers in 2020. The company grew strongly in the last three years. Demand was boosted by the WFH trend as it required greater spending in endpoint security. Historically, CRWD have primarily sold to large organizations, but have increasingly made inroads in the SME market. Revenue through channel partners has grown to 83% of total revenue.
Security solutions are generally very sticky. The gross retention rate was reported to be 98% in FY’21. The dollar-based net retention rate (DNBR) has risen to 125.3 %. This number reflects customer renewals, expansion, contraction, and churn. It is above 100% as the customer base at the beginning of a year will purchase additional modules in the following 12 months.
The Geographical breakdown of sales is as follows:
United States- 74.1%
Europe, Middle East, and Africa -14.0%
Asia Pacific - 7.8%
Other - 4.1%
The company believes there is a great opportunity to increase non-US sales. They expect the US will be 50% of their sales in the long run.
Acquisitions and Inorganic Growth
Historically, the strategy has been to grow organically. However, they have done acquisitions as they move beyond endpoint security and broaden their offerings. In September 2020, CRWD bought Preempt Security for ~$90 mn which developed real-time access control and threat prevention technology. They also acquired Humio for $400 million. Humio is a cloud-native observability platform that helps organizations collect, store, and analyze machine data.
Business Strategy
CrowdStrike have built up a strong position in Endpoint Protection. IDC's Annual Worldwide Modern Endpoint Security Market Shares Report for the third consecutive year found CrowdStrike was the largest, with a 17.7% market-share, outpacing all vendors by posting the largest increase in revenue and market-share in 2022.
CrowdStrike now wants to expand further into the SME market. The low cost Falcon Go bundle (noted above) is a key element in this. “ We have had tremendous initial success with our Falcon Go bundle, specifically designed as a starter package or landing point for smaller businesses with 100 endpoints or less that may be more price sensitive. We have already added over 1,000 net-new customers through the program in two quarters.”
CrowdStrike wants to increase non-US sales from the current 28% to 50% in the medium term.
CrowdStrike has been quietly pivoting their EPP platform (protecting systems and devices) to also protect container & serverless workloads (protecting apps & services across cloud providers). New Modules including Humio have been a critical part of this.
AI
In the last six months, many companies have been talking about the role AI plays in their business models. As CRWD has been collecting and analysing (threat) data for over a decade, their claim to be an AI company are stronger than most.
“We started the Company leveraging big data AI to be able to identify threats that have never been seen before and prevent against those. We continue to build out our AI capabilities across all of our different modules with the massive data and telemetry that we collect every week.”
“CrowdStrike is uniquely positioned to benefit from this new technology (AI). Our dataset spans petabytes and captures trillions of new events daily from our global fleet of sensors. Combined that with our over 10 years of attack data and threat graph that has been paired with high-quality human analysis from OverWatch, complete intelligence and incident response services and you get unrivaled telemetry.”
Having 10 years of data and experience in processing and analysing it and improving data analysis in an iterative way represents a moat. It is a business advantage that a rival would find difficult to replicate easily.
The company is probably correct when it says “CrowdStrike has a sustainable data advantage, the most powerful and unique set of correlated human and machine-generated data across all of cyber.”
AI may help companies but it will be tool also used by rogue actors.
“We expect that the adoption of LLMs will lower the barrier of entry for malicious actors to create sophisticated cyber-attacks. Generative AI is expected to make it even easier for less advanced attackers to crack nation-state-caliber campaigns.”
“This will catalyze even greater demand for modern cyber security technologies like Falcon. From a protection standpoint, we see generative AI as a democratizing force by dramatically lowering the learning curve for practitioners transforming even a novice analyst into a power user.”
“We introduced Charlotte AI, an exciting new generative AI security analyst utilizing CrowdStrike's high fidelity data advantage. We believe Charlotte AI will power a newly minted Tier-1 analyst to yield the results of an advanced Tier-3 analyst, the net benefit to the customer, faster results, better security outcomes, and lower overall costs.”
“As I mentioned, when we launched Charlotte AI in public preview is the fact that it really is a virtual analyst, a SOC (security operations centre )analyst, which are super expensive and hard to maintain. So for our purposes, when we look at the total value to a customer, if we can create more virtual analysts, just as an example that takes eight hours of work and compresses it into 10 minutes.”
“We teamed up with AWS to develop powerful new generative AI applications that help customers accelerate their cloud, security, and AI journey. Through this initiative, CrowdStrike and AWS will bring together their solutions and teams to keep customers safe across a range of AI services, while meeting stringent security requirements. CrowdStrike already has a leadership position in helping protect AI innovators.“
The Magic Quadrant Rankings
The products and services offered by technology companies are assessed by numerous independent third-party analysts such as Gartner, Forrester, and IDC. Their results are presented in terms of quadrants. An example is shown below. The higher the company’s position and the further to the right, the better the company is rated.
Grids like this are created for characteristics of products and services and companies cherry pick those which show them in a good light. CRWD is no exception.
Frost & Sullivan granted CrowdStrike its Leadership Award in Endpoint Security for 2022.
The CrowdStrike Falcon Platform achieved 100% protection accuracy and 100% legitimacy accuracy with zero false positives, winning SE Labs’ first-ever endpoint detection and response (EDR) ransomware detection and protection test
The Falcon Platform detected and blocked 100% of ransomware files during testing, which involved both direct attacks with 270 ransomware variations and deep attack tactics, with 10 sophisticated attacks mimicking observed tactics of cybercriminals
SE Labs AAA Enterprise Advanced Security (Ransomware) Award.
SE Labs a leading independent computer security testing organization — conducted a new test for Ransomware protection. It found Falcon platform provides effective protection against ransomware and sophisticated breaches
The Falcon platform scored a perfect 100% protection accuracy rating, having detected and blocked every ransomware attack including the unknown variants. The Falcon platform also achieved a 100% accuracy rating in identifying legitimate applications and websites, and in deep attack testing detected all 10 attacks, exposing the ransomware in every case and offering thorough insight into testing threat chains.
Overall, the Falcon platform received a total accuracy rating of 99%, which indicates it is extremely effective in protecting from subtle attacks and accurately identifying non-malicious objects such as web addresses and applications. As testing was performed in real-world configurations, accuracy means the evaluation also tested for false positives — and the Falcon platform generated absolutely none.
High accuracy means no inconvenience for users attempting to use legitimate websites or apps; it means no downtime resulting from the investigation of false positives; it means security operations center (SOC) analysts can spend more time addressing real detections in particular and less time operating security solutions in general — all of which serve to lower organizations’ TCO and minimize security-related business interruptions.
According to SE Labs:
“CrowdStrike Falcon performed exceptionally well at protecting against known and new variants of ransomware, as well as tracking network attacks that concluded with ransomware payloads.”
The full SE Labs report, including details on how the Falcon platform was tested, is available here.
CrowdStrike has an overall rating of 4.9 out of 5, the highest rating of all among vendors named a November 2019 Gartner Customer’s Choice for the endpoint protection platforms market, based on 188 reviews, as of 31 October 2019.
Key current features driving the Cybersecurity market
The threat is becoming more potent. The sophistication of adversaries continues to increase as services of well-funded nation-states, technically advanced criminal organizations and hackers use advanced, easily obtained methods of attack – including non-malware based attacks that exploit user identities and credentials. This year has seen an increase in activity from Russia particularly after the invasion of Ukraine. The typical attack cycle starts with attackers attempting to penetrate endpoints to establish a beachhead. Once inside, they steal and exploit legitimate credentials/ identities to escalate privileges, move laterally and progress and attack, often downloading malware or ransomware. At this stage, the adversary is able to encrypt, destroy, or silently steal sensitive data. As these are non-malware attacks, legacy systems are ineffective and need to be (urgently) replaced.
The move to Hybrid and Remote Workforces creates a larger target. As companies and organisations increase workforce mobility, and rapidly grow their connected devices, bad actors have a much larger surface to attack. This trend was accelerated significantly due to WFH in the COVID-19 pandemic. In addition, the target surface has increased as companies have moved data and workloads to the Cloud.
A growing skills Gap. Trained cybersecurity professionals are in short supply. Incumbent cybersecurity teams are often overwhelmed by the velocity of attacks.
The need to simplify. Organizations are increasingly looking to reduce the complexity of their IT stack. Modern security requires fewer point products and fewer agents. Increasingly, organizations are looking to standardize on trusted platforms that deliver an immediate return on investment and lower the total cost of ownership.
The Competitive landscape
The competition that CRWD faces can be divided into four slabs
Legacy companies (Symantec, McAfee, Trend Micro, Sophos, Kaspersky etc.),
Next-Gen Companies ( Carbon Black, Cylance, SentinelOne ) CrowdStrike is on this category.
Microsoft - the 600lb gorilla in the space
Platform Plays (Avast, Cisco, FireEye, Palo Alto Networks, Check Point Software, Fortinet and Zscaler), Many Platform plays started as Firewall suppliers but are moving into cloud security and security software products.
The rise in interest rates and the turn of the cycle should mean that private equity should not fund many new companies in this field. They are more likely to focus on dealing with those already in their portfolio such as Wiz, and Deep Instinct.
Legacy companies had a 73% market share in 2015 but this has rapidly fallen to below 20%. Legacy companies have belatedly launched cloud offerings but may nonetheless slide into irrelevance.
MSFT is the largest player with a 26% market share. Next-Gen companies have a 13% share. The Platform plays and other companies probably account for ~30% of the market.
The Legacy companies have lost market share rapidly and others, especially Microsoft, have gained it.
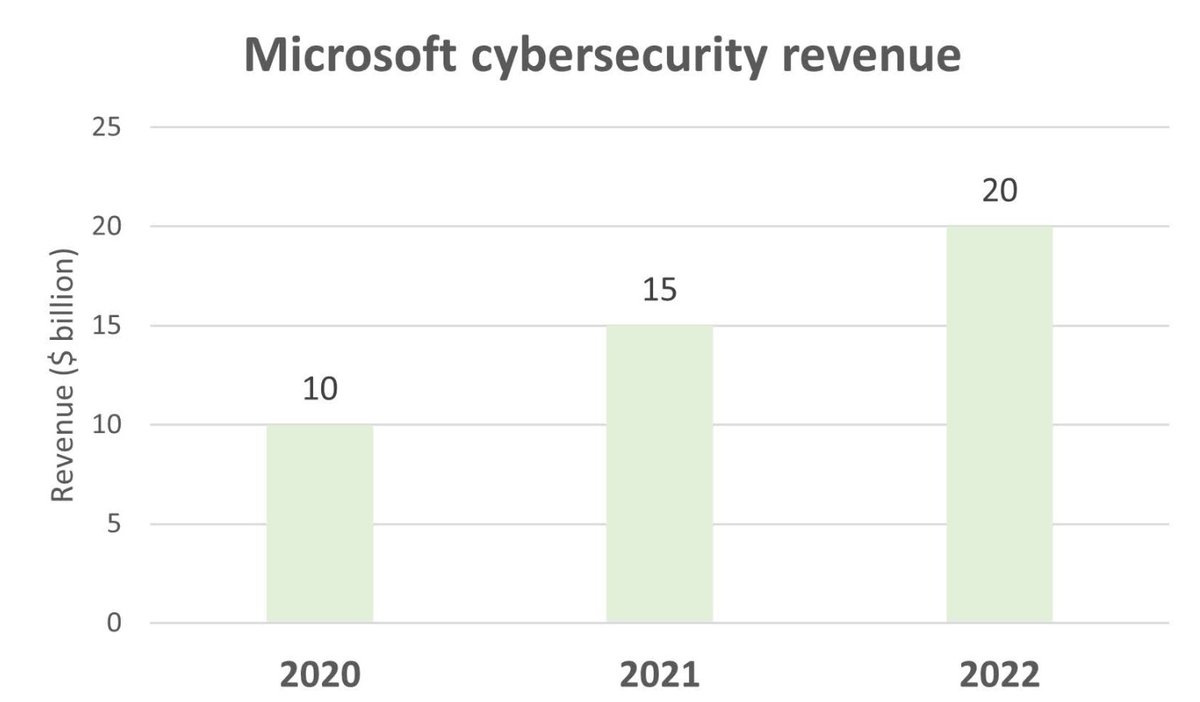
Microsoft has become a behemoth very rapidly. It reported $20bn revenue from security segment in 2022, growing 33%-40% YoY; the annual increase itself is almost 2X CRWD’s current annual revenues. For Microsoft, security is less than 10% of its total revenues.
Microsoft is a formidable competitor and has the advantage of huge size and scale. It can fight for a long time knowing it can win any competitive war of attrition.
Customers want to reduce costs and consolidate and reduce the number of vendors. Most of the large companies are currently growing revenues strongly but consolidation in the industry is likely soon.
Cybersecurity startup Wiz which is backed by Blackstone and Sequoia said in August it was looking at taking over SentinelOne. This proposal was soon abandoned but the proposal is a straw in the wind. Cylance was bought by Blackberry in 2019 but there are rumours they are looking to sell it. There are also rumours about the future of SentinelOne, which is a younger version of CRWD. Such rumours unnerve potential buyers who are looking to make long-term commitments and are ruthlessly exploited by competitors.
Other companies such as Palo Alto Networks and Fortinet started off as Firewall companies but are now looking at Cloud Security. Fast growing Zscaler has been more focused on securing data as it moved in the network rather than the endpoint.
The likely continued decline of Legacy Companies will mean there will be a lot of market share to be fought over in the short-term. Symantec’s Enterprise customer count exceeded 100,000 in 2019 when it was acquired by Broadcom. McAfee’s Enterprise customer count is currently still about 50,000 despite years of market share loss.
CrowdStrike can increase customer count from 23,000 to 50,000-100,000+ over time. So there is a good chance they can increase revenues by winning market share.
However, they face competition. We have also looked at Palo Alto Networks and Zscaler. Both are growing strongly and have been free cash flow positive for many years and are profitable at the net level in 2023.
It is likely that all these (Palo Alto Networks, Zscaler, CRWD) and others will grow revenues while legacy companies and others like Cylance, SentinelOne will lose market share.
The more difficult question is what to think about Microsoft. We are an investor in Microsoft and admire the company. Our initial thought is similar to one expressed by a former CrowdStrike sales representative quoted below:
“I'll start with the biggest no-brainer to maybe not go with CrowdStrike. Microsoft is one of the best in the business at selling Enterprise License Agreements (ELA), getting customers who'll sell 365, who'll do a bunch of other stuff. They can land and expand pretty much better than most any other company I've ever seen before. They create these licenses. They continue to try to get sticky with customers in that capacity so customers start to work with Microsoft and the easy answer is, "We've already got Microsoft. Why would we even entertain somebody else like a CrowdStrike?" for example. That would be probably one where I would say it might be harder for CrowdStrike to break in some of those accounts.”
Microsoft is large company which has direct and indirect relationships with almost all companies and organisations globally. They already supply many products and services and have simply added Cybersecurity products to this unrivalled pipeline.
However, Microsoft has suffered a number of well-publicised major hacks. On the 8th September, Microsoft explained “a series of unfortunate and cascading mistakes allowed China-backed hacking group to steal one of the keys to Microsoft’s email kingdom that granted near unfettered access to U.S. government inboxes in July” . An article on this can be read here.
A Forbes article from August 2023 interviews the Chief Security Officer (CSO) of CrowdStrike and talks about Microsoft’s security failings. It notes “Customers, competitors, and even U.S. senators have stressed that these issues expose companies and government agencies to significant risk and raise questions about the company's practices in both cybersecurity and competition.”
The Forbes piece argues that a company which writes millions of lines of software code should make sure that the code is fully secure rather than sell security software to help clients deal with breaches of the poorly written code. It implies that by being in the Cybersecurity business, Microsoft has a serious conflict of interest. This article can be read here.
CrowdStrike seems particularly bold in its attacks on Microsoft Security Products. In their recent earnings calls, they cite examples of customers who have bought CRWD Modules in preference to Microsoft’s products.
“We gained 3.8 percentage points, which is more share gain than any other vendor including outpacing Microsoft. And what customers are really telling us is that, Microsoft good enough security is not good enough and we've been winning because of our coverage across multiple operating systems, the complexity of Microsoft six consoles. In fact, just today alone, they had six signature updates.”
“This company had initially chosen Microsoft and replaced existing AV (Anti-virus) products across their estate, quickly ran into trouble when they discovered that Microsoft Defender cannot be fully deployed within their heterogeneous environment, leaving their service vulnerable. Unfortunately, it did not take long for threat actors to find these gaps and breach their environment. During engagement, the customer found that CrowdStrike Falcon provided 2.5 times more coverage than Microsoft Defender and was much simpler to operationalize. It quickly became obvious to this company why AI protection was far superior to signature-based technologies and they needed world-class protecting across heterogeneous operating systems. The system also determined that excluding the cost to remediate the breach, Defender cost twice as much and would still fall short of the functionality, simplicity and efficacy of Falcon. Having loss faith in Microsoft's low-cost, good enough promise this new CrowdStrike customer adopted Falcon…”.
“CrowdStrike won a large client this quarter from Microsoft Defender after they failed to protect the client in a multi-cloud environment. It turned to CrowdStrike’s incident response service to more than double coverage capacity while cutting costs by 50%. Microsoft breaches continue to be a large lead generator for CrowdStrike new logos and incident response business. And for every $1 in incident response business, CrowdStrike enjoys more than $6 on average in up-selling those customers to other modules.”
“We won a leading financial institution in the Fortune 50. The client consolidated on Falcon and replaced 4 disparate vendors in doing so including Symantec and Trend Micro. It tested CrowdStrike vs. all other relevant next generation bids and thought it was clearly the best option.”
“A global financial technology company replaced 8 siloed security vendors with Falcon. Displacements included Microsoft Defender and Carbon Black. It also bought Falcon’s log management module in a sign that Humio is resonating with large clients. ”
“A major auto manufacturer that tried but failed to consolidate their security on Microsoft E5. This company's security team quickly realized Microsoft's complexity, multiple consoles, lack of integration, miss detections and complex deployments hampered their ability to defend themselves and consolidate. This customer is now consolidating on the Falcon platform with Falcon Complete for Endpoint, Identity and Cloud. Now with a single agent, single user interface and single platform, they have complete visibility across their end points, cloud and identities and the ability to stop threats in real time. By moving from expensive Microsoft E5 to CrowdStrike, organizations can save 50% plus per user per year on Microsoft licensing costs, adding up to millions of dollars of saving.”
“A manufacturing giant tried and failed to consolidate on Microsoft and its E5 licensing. It moved to CrowdStrike for superior efficacy and 50% per year per using savings by shedding licensing costs and complexity.”
“We won a 7-figure deal to standardize a new construction client on Falcon. This change allowed the client to cut spend with several vendors by 60% and to eliminate many more vendors.”
“The Identity suite won a Fortune 500 client and displaced 4 vendors including Microsoft and SentinelOne.”
There are at least two claims being made here by CRWD.
Customers are reducing the number of siloed products from Legacy providers and others. CrowdStrike is being asked to pitch along with other next-generation companies and often wins the order.
Companies have often been persuaded to buy Microsoft Defender and ES2 but found them wanting and suffered breaches. The CrowdStrike Incident Response team is called in to investigate the problem. This often leads to the customer switching to CrowdStrike Modules which are cheaper and and more effective.
So these example and CRWD’s numbers suggest they will grow strongly in the medium and long-term as the market expands, vendors are consolidated and they win some share against Microsoft.
The Company claims it has a clear mandate from customers. The latter want to reduce cost and headcount, reduce the number of point products, reduce complexity and simplify operations.
CRWD is well positioned to benefit as enterprises increasingly prefer platform approaches to cybersecurity solutions, seeking out cybersecurity providers offering comprehensive portfolios and enabling simplified cybersecurity management, fast ROI, and lower total cost of ownership.
Summary
CrowdStrike is a fast growing next-gen cybersecurity company.
The Company has a successful “land and expand” strategy. Evidence of this in the steady increase in the modules purchased by existing customers .
It has been a strong generator of free cashflow and is expected to make a net profit in the current year.
The company is likely to grow strongly in the next few years as it continues to gain market share from legacy players. It could also gain share by winning customers in competitive bids against established players including Microsoft.
Conclusions
We think the market will grow and there will be enough room for a few winners.
If earnings per share grow at about 30% for the next three years, it is likely CRWD’s 3-4 year forward Price Earnings ratio will be about 25 times. This does not seem too high for a company with the current and prospective economic characteristics of CrowdStrike.
We need to do a DCF calculation to get more definitive fix on the valuation.
The sector is attractive but the way to get exposure is with two or three stocks. We already have Microsoft in the portfolio and will work to add two more stocks selected from the likes of Crowdstrike, Zscaler, Palo Alto Networks and Fortinet.
Annexe 1 : Zero Trust
We noted above that Legacy systems were based on the Trust and Verify model. Once people had access to the network they could be trusted throughout the network.
The new security paradigm is Zero Trust. The premise is that neither external networks (the internet and SaaS services) nor the internal network (enterprise network & WAN) should ever be trusted!
You never trust a user requesting access to a particular service. Users must establish who they are (authentication), and then the system determines the rights of that user to access the given service (authorization).
Once BOTH identity and access rights have been established, the Zero Trust service acts as a proxy to the service, creating an ephemeral network connection to the requested service only. Once the user is done, the temporary connection from user to service can be severed.
Every service is individually secured, instead of being among a pool of services in a trusted network. Zero Trust inherently prevents lateral movement, as users cannot access anything else in that connection except the service they originally requested. It also prevents privilege escalation, as the user only has the access rights determined by the identity system when the connection is established.
This is a fundamentally different approach compared with traditional network security architecture. Unfortunately, it is also a lot more complex to set up and manage, due to the intricacies of how to manage services, users, and access rights so granularly, how to manage the ephemeral network connection, and then how to monitor and audit all of it. Cloud-native cybersecurity services like those developed by CrowdStrike are able to provide turnkey solutions that can do it all.
Identity-based Access
Zero Trust has solved how to better secure internal resources but what happens to those resources moving to the cloud. Cloud-native SaaS services began to appear that could solve this issue. Zscaler was a pioneer in this area,
The key is tying the access system into an identity provider that could better handle the identity and access tracking (authentication and authorization) part of the process. There were existing Identity and Access Mgmt (IAM) services from cloud-native providers like OKTA, managing workforce security and providing features like Multi-Factor Authentication (MFA).
Major Zero Trust providers include Zscaler, Palo Alto and Cisco. These platforms must hook into a wide variety of authentication stores in order to have wide applicability to whichever IAM tool that its customers prefer.
Context-based Access
While Zero Trust originally depended on identity, it expanded to include other aspects that could provide more context about the request beyond only the identity of the user, such as the device they use, the location they are in, or the network they used.
A remote workforce tends to use enterprise-owned devices (mobile and laptops) for performing their work. Enterprises using an IAM services tare relying upon EPP/EDR platforms like CrowdStrike to manage security over their pool of devices. They use Endpoint Protection Platforms (EPP) to protect all enterprise-owned devices, and Endpoint Detection and Response (EDR) systems to manage the security over their entire fleet of devices.
This total view over a device's status in the pool of an enterprise's device network is known as Device Posture. Like Identity, it has become a vital component of the Zero Trust ecosystem. Zero Trust platforms could now rely on both IAM and EPP/EDR partners to provide better vision into the user and the device utilized, and partnerships started quickly forming.
CrowdStrike has partnerships Zero Trust platforms and providers such as Zscaler. CrowdStrike is extremely well positioned as a vital partner in Zero Trust.
Continuous Analytics
Security does not stop with simply securing user access at the start of the request – it had to remain secure throughout the lifespan of the request. By leveraging the signals they can receive from the identity & device posture partners, as well as from the traffic going through the ephemeral network connection, Zero Trust platforms can assess risk and trust continuously through the lifespan of the connection, and can dynamically adjust itself based on changes in context or if it detects abnormal behaviors.
Continuous Analytics is about utilizing ML/AI over all the known identities and devices to establish a base line of expected behavior (what a user or device normally does), then continuously profile the session to flag any risky or anomalous activity it sees.
The process is known as User & Entity Behavior Analytics (UEBA), and the goal is to flag deviations from the norm in an internal risk score. Rules are built around those risk scores to trigger actions, such as requiring additional forms of identification during authentication (requiring MFA), stopping an action, or severing the connection.
This means that Zero Trust can take an adaptive posture that is proactive, instead of reactive. Access is conditional based on the risk scoring, and it can dynamically adapt if it determines the risk level is too high, and perform actions like blocking a download or terminating access completely if warranted.
Does a user normally always log in from a variety of networks in London during the daylight hours, but is now appearing on one from Moscow at midnight?
Does a user normally download megabytes of files, but is now downloading hundreds of gigabytes?
Does a user normally use one device (a laptop), but is now coming from an unexpected one (a web server)?
Continuous Analytics are extremely helpful at detecting compromised systems and user accounts, as well as insider threats, brute-force attacks, changes in permissions, and attempts to access unauthorized areas. CRWD is well placed to benefit as the world moves to Zero Trust.
“Eighty percent of breaches today use stolen credentials and identities. Stopping these advanced attacks requires a Zero Trust approach that delivers true end-to-end protection across workloads, identities, and data. CrowdStrike is able to natively enforce Zero Trust protection at the device layer, the identity layer, and the data layer, extending our bold vision for security by driving modern Defense in Depth to the enterprise.”
Annexe 2 : Dual class share structure
CrowdStrike has a dual class stock structure: Class B common stock has 10 votes per share, and Class A common stock has only one vote. This has the effect of concentrating voting control with original shareholders including executive officers, employees, directors, principal stockholders, and their affiliates. Let us call these holders the early insiders.
Future transfers by holders of Class B common stock will generally result in those shares converting to Class A common stock, which will have the effect, over time, of increasing the relative voting power of the early insiders.
As of January 2023, the early insiders held 38% of the voting power of the outstanding stock.
Dual class structures are often a red flag as they allow a group of shareholders to have disproportionate influence. However, it should also be noted that Berkshire Hathaway also has a dual class stock structure.
Annexe 3 : Various Revenue and other measures
Annualised Revenue Rate (ARR) is calculated as the annualized value of customer subscription contracts on the measurement date, assuming any contract that expires during the next 12 months is renewed on its existing terms.
Dollar-Based Net Retention Rate (DBNR) DBNR compares the ARR from a set of subscription customers against the same metric for those same cohort of subscription customers from the prior year. DBNR rate reflects customer renewals, expansion, contraction, and churn. As customers buy more modules over time, the DNBR is more than 100%. The target is 120% and it is currently ~125%.
The SaaS Magic Number is a ratio that indicates a company's operational efficiency and long-term sales and marketing sustainability. It is calculated by determining the amount of annual recurring revenue increase generated for each dollar spent on sales and marketing. It should be more than 1 if marketing spend is having a positive impact.
“I think we’ve done a great job in being able to manage that growth, not at all cost, but with a realized at the bottom. I mean, operating at a Magic Number above 1 and a rule of 81 on a free cash flow basis are best in class.”
Annexe 2 The key benefits of the Crowdstrike Falcon
These include:
•The Power of the Crowd: The crowdsourced data enables every customer to benefit from contributing to the Security Cloud. As more high fidelity data is fed into the Security Cloud, the AI models continue to train and improve, increasing the overall efficacy of the Falcon platform. This creates a powerful network effect that is a key differentiator in CRWD’s efforts to gain more customers. The Threat Graph is able to contextualize and turn this data into action, automatically delivering protection to every customer.
•High Efficacy, Low False Positives: The vast telemetry (incoming data) of the Security Cloud and the best practices employed in continually training the AI models results in industry-leading efficacy rates and a low number of false positives.
•Consolidation of Siloed Products: Integrating and maintaining numerous security products
creates blind spots that attackers can exploit,
is costly to maintain and
negatively impacts user performance.
The cloud-native platform approach gives customers a unified approach to address their most critical areas of risk seamlessly. CRWD empower customers to rapidly deploy and scale industry leading technologies across many functions from a single platform.
Reducing Agent Bloat: The single intelligent lightweight agent enables frictionless deployment of the platform at scale, enabling customers to rapidly adopt technology across any type of workload running on a variety of endpoints. The agent is non-intrusive to the end user, requires no reboots and continues to protect the endpoint and track activity even when offline. Customers can adopt multiple platform modules to address their critical areas of risk without burdening the endpoint with multiple agents. Legacy approaches often require multiple agents as they layer on new capabilities. This can severely impact user performance and create barriers to security.
Rapid Time to Value: The cloud-native platform was built to rapidly scale industry- leading protection across the entire enterprise, eliminating lengthy implementation periods, and professional services engagements that next-gen and legacy competitors require. The single agent approach enables customers to activate new modules in real time.
Elite Security Teams as a Force Multiplier: As adversaries continue to employ sophisticated non-malware attacks that exploit user credentials and identities, automation and autonomous security are no longer sufficient. Stopping today’s sophisticated attacks requires a combination of powerful automation and elite threat hunting. Falcon Complete provides a monitoring, management, response, and remediation solution to CRWD’s customers and is designed to bring enterprise level security to companies that may lack enterprise level resources.
CRWD can see attacks across our entire customer base, their expertise is enhanced by their constant visibility into the threat landscape. Additionally, the insights of the OverWatch team (A human team which also look over the data and monitors emerging threats) can then be leveraged by the Falcon platform to further enhance its autonomous capabilities, creating a positive feedback loop for customers.
Alleviating the Skills Shortage through Automation: CrowdStrike automates manual tasks to free security teams to focus on their most important job – stopping the breach. The Falcon Fusion module automates workflows to reduce the need to switch between different security tools and tasks, while the Falcon Insight XDR module provides a unified solution that enables security teams to rapidly and efficiently identify, hunt, and eliminate threats across multiple security domains.
Lower Total Cost of Ownership: The cloud-native platform eliminates customers’ need for initial or ongoing purchases of hardware and does not require their personnel to configure, implement or integrate disparate point products. Additionally, CRWD’s comprehensive platform reduces overall personnel costs associated with ongoing maintenance, as well as the need for software patches and upgrades for separate products.
Annexe 4- Some definitions
Endpoint detection and response (EDR)- Definition: EDR refers to a category of tools used to detect and investigate threats on endpoints. EDR tools typically provide detection, investigation, threat hunting, and response capabilities.
Extended detection and response (XDR)- Definition XDR collects and automatically correlates data across multiple security layers – email, endpoint, server, cloud workload, and network. This allows for faster detection of threats and improved investigation and response times through security analysis.
CRWD is a pioneers of EDR and has extended into XDR
Managed Detection and Response (MDR)- Definition - MDR is a cybersecurity service that provides organizations with a team of experts who monitor the client’s endpoints, networks and cloud environments and responds to cyberthreats 24/7.
Of the top 25 MDR vendors by market share defined by Gartner, 88% have built their MDR services on top of the Falcon Platform. This indicates that Falcon is the professionals MDR platform of choice.
Managed service provider (MSP) -definition- An MSP delivers services, such as network, application, infrastructure and security, via ongoing and regular support and active administration on customers' premises, in their MSP's data center (hosting), or in a third-party data center.
CrowdStrike recently entered into a strategic partnership with Pax8, the leading MSP cloud marketplace with over 30,000 MSP partners across North America, EMEA, and APJ that serve the SMB market.
Pax8's MSP partner base will now be able to protect their end-customers with the same cutting-edge XDR technology selected by the world's largest enterprises.



















Sanjiv, this has been an awesome read. Thank you for the effort and analysis!